Executive Summary
As financial planning slowly transitions into the digital age, and increasingly common discussion is whether to transition client information to the cloud, where it will be hosted on servers in a data center, instead of the planner's office. Given the frequency of high profile data breaches announced in the media, is it really safe to move client information out of the office? Yet in most cases, the planner's office, and the client's home, are not nearly as secure as we make it out to be. Data centers have fences, guards, sophisticated security monitoring, and intrusion detection systems built to rebuff those trying to access data inappropriately, while the client's best data defense is often little more than opening the door of the mailbox, and planning firms often lack the size and scale for truly effective security either. In point of fact, most firms don't even have the systems to know if they've been "hacked" in the first place, and wouldn't know until clients began to report identity theft problems! In addition, a persistent media bias that highlight major companies with data breaches but not small businesses that lose client files, may be misdirecting focus and causing us to misjudge the relative safety of the options. Which means ultimately the reality is that, notwithstanding the occasional high profile story, cloud security may actually still be far more effective at protecting client data than we realize!
The inspiration for today's blog post is a recent conversation I had with another financial planner, who suggested that he would "never" transition his client data to the cloud, and encourages all of his clients to avoid doing so as well, suggesting that the security could never be as safe as paper files and physical documents that can be kept on-site at the planner's firm and/or the client's home. "Just look at the recent LinkedIn hacking, the latest example of how unsafe data is on the web!" "But is electronic data really less secure," I replied, "or is this just a classic example of behavioral bias gone bad?"
Data Security And The Availability Heuristic
Behavioral finance research has long demonstrated a mental heuristic called the Availability Bias, where we make a judgment about the probability of an event occurring based on how easily we can recall an example of the event. For instance, when a plane accident occurs and hits the headlines, people tend to fly less and drive more, perceiving an uncomfortably high probability of an air disaster, even though the objective data overwhelmingly demonstrate that the risk of an accident while driving is radically higher than the risk of a plane accident. Similarly, news of a shark attack - and for those who have seen it, the movie Jaws - causes us to regularly overestimate the probability of a shark attack, even though the reality is that only a few dozen people in the world are attacked by sharks every year (and only a handful of those are fatal); in point of fact, it's actually 3 times more likely to die by drowning at the beach than a shark attack, and approximately 30 times as many people die every year by a lightning strike than at the jaws of a shark! In the case of digital data security, we potentially suffer from a similar problem; due to the disclosure requirements on companies in the event of a data breach and the reporting of the media, even relatively infrequent high profile data breaches feel as though they're reported with some regularity. As a result, it is far easier for the average person to recall a data breach from a high profile company than it is to recall other ways that data can be lost or stolen.
What's Really More Secure?
So what's really more secure for clients trying to send, receive, and access data? The graphic below shows an example of the two alternatives.
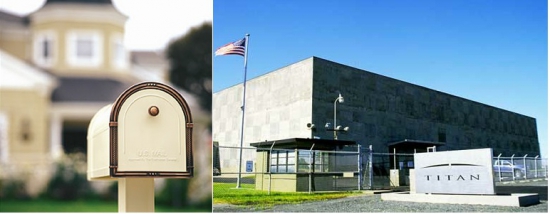 Viewed from this perspective, it seems somewhat absurd to suggest that the mailbox on the left, unmonitored, unlocked, and unsecured in any way, could possibly be more secure than the facility on the right, a "server farm" facility in Moses Lake, Washington replete with guards, a fence-and-barbed-wire perimeter, state-of-the-art security monitoring, and extensive intrusion detection capabilities to identify and rebuff a physical or electronic attack. In fact, perhaps the greatest irony is that if someone stole an important piece of information from the client's mailbox, it's unlikely the client would ever even know, assuming that it must have been "lost in the mail" instead... at least, until/unless an identity thief began to act upon the information. While the file room of a planner firm may be somewhat more secure than a client's mailbox, it's still far less secure than a typical server farm that would be used to host client data on the internet. For instance, just a few recent security breaches I've heard about from various financial planning firms include:
Viewed from this perspective, it seems somewhat absurd to suggest that the mailbox on the left, unmonitored, unlocked, and unsecured in any way, could possibly be more secure than the facility on the right, a "server farm" facility in Moses Lake, Washington replete with guards, a fence-and-barbed-wire perimeter, state-of-the-art security monitoring, and extensive intrusion detection capabilities to identify and rebuff a physical or electronic attack. In fact, perhaps the greatest irony is that if someone stole an important piece of information from the client's mailbox, it's unlikely the client would ever even know, assuming that it must have been "lost in the mail" instead... at least, until/unless an identity thief began to act upon the information. While the file room of a planner firm may be somewhat more secure than a client's mailbox, it's still far less secure than a typical server farm that would be used to host client data on the internet. For instance, just a few recent security breaches I've heard about from various financial planning firms include:
- No alarm system for the office
- Alarm system for the office, but did not cover the crawl space above the drop-ceiling which the thieves used to enter
- Alarm system for the door... so the thieves simply cut a hole in the drywall next to the door and walked right in
- Server room was locked, but the door hinges were on the outside... so the thieves simply popped the pins out of the hinges and took the door off!
- Servers had strong passwords to prevent someone from easily logging in to take data... so the thieves simply wheeled the entire server rack out the front door and into the van, and hacked into it on their own time!
- Cleaning crew had access to unlock doors and turn off alarms... so a desperate employee of the cleaning crew opening the file room and took some client files and tried to sell the client Social Security numbers.
- Office was secure and alarmed... except when the weekend cleaning crew came in. While the cleaners did nothing wrong, the open office allowed someone dressed in a suit pretending to be an employee of the firm walked right in, took a company laptop with client information, and walked out as though it was his!
Notably, these kinds of security breaches are difficult to fend off entirely... at least, for a small company that is not primarily in the business of secure data and that has limited economies of scale to establish an entirely secure facility. In the case of a company whose sole business is the secure hosting of client data, on the other hand, such security breaches are far less common. In fact, the facilities are generally so secure, that virtually all "attacks" happen digitally and virtually, not physically. In addition, such attacks tend to simply target "stealing" as much data as possible, often untargeted, in the hopes of getting some useful information that can be capitalized upon. In hosted data facilities, it's actually radically more difficult to steal a particular individual's data (compared to stealing from that individual's mailbox, or client file from the planner's office); as a result, thieves often just try to copy as much information as they can, and sort out later whether/what can be used. Unfortunately, the one caveat of large data centers is that because they are data rich, they do become especially appealing targets for data thieves.
Not All Cloud Security Is The Same
It's also important to note that not all cloud security is the same. Just as with any other security situation, some facilities and storage centers are better protected than others. The standard for client data in financial services is called "SSAE 16 Type II" (previously known as "SAS-70 Type II"), which represents a certain level of security rigor that is audited by a third party firm to test for proper controls on data. Notably, many financial firms that service advisors and their clients maintain client data on SSAE 16 Type II data servers, such as Orion Advisor Services and Tamarac. Similarly, it's also worth noting that not all data breaches are the same, either. For instance, while it was highly publicized, the reality is that the recent LinkedIn breach may not have compromised any data beyond just user names and passwords; no credit card information, Social Security numbers, or other identity-related information, is known to have been violated. Instead, the greatest risk from the LinkedIn incident may simply be client security on other platforms if the client uses the same email address and same password for other, more secure websites that do have important personal data. Which means in the end, any data breaches as a result of the LinkedIn event would be primarily a result of poor password use by consumers, not the LinkedIn breach itself (you should not have the same password for a website like LinkedIn that you do for your secure banking, for example). The bottom line is that true data breaches that really compromise client information are not nearly as common as the headlines make it appear. The fact that advisors don't hear about the thefts from the offices of their peers, the mail stolen from client mailboxes, and don't even have the software to detect if their own servers are hacked (so they wouldn't know even if it did happen!) may mean data breaches in the office and at the client's home aren't visible, but certainly doesn't mean such alternatives are actually more secure. In fact, by any classic measure of security, they're actually far less, especially if client data is hosted in a facility that is genuinely secure and has been audited and reviewed to substantiate that. So what do you think? Do you host your client data in the cloud, or on your own servers? Do you view your client files and mailing documents to clients as being more or less secure than emailing them or housing them electronically? Have you ever been subject to a physical or virtual data breach? Would you know if you had? Would your clients?



Good timing on this post, Michael.
The Journal of Financial Planning published my July contribution online, “How to Stay Safe When Using the Cloud.”
It provides a ten-item checklist that covers many of the due diligence topics all advisors should review when evaluating a cloud provider.
http://j.mp/M13U45
Is The Cloud really a more secure place for your client data yeah i agree with this cloud is better than storing them on an in-house server or off site.outstanding just what i was looking for !
@CyrilAndreew Great post. Very unique concept you have shared here. Really the cloud is more secure place for your clients data. Also keep in mind the company of cloud computing because security does metter on company like how they handle it and where they store the data.